Benefits of Implementing SOAR in Your Cybersecurity Strategy

With SOAR, your security team accesses a single console that provides all the necessary intelligence and controls.
A SOAR platform integrates a broad range of tools for cloud security, forensics, malware analysis, data enrichment, threat intelligence, vulnerability and risk management, and incident response.
This prevents security teams from juggling consoles and tools while offering a comprehensive view of the incident on a single dashboard.
Reduced False Positives
False positives constantly burden security teams, often generating an alert at the slightest provocation. SOAR automates these processes, allowing analysts to spend less time dealing with false positives and more time investigating actual threats.
SOAR also provides security analysts with playbooks to help them respond quickly and efficiently. These playbooks are created based on several data-driven factors, including threat intelligence providers, alert types, and response actions.
The playbooks are designed to guide analysts to the correct response action(s) and provide a consistent approach to threat analysis. This saves time and improves efficiency, while analysts learn from their playbooks and can enhance their security skills.
Moreover, SOAR enables you to automatically queue and prioritize alerts, letting you see what needs your attention first. It will also display organized alert details, such as IP addresses, domain names, and file hashes, making it easier to find important information.
Another benefit of SOAR is that it seamlessly allows you to switch between different datasets and information sources. This can reduce the time it takes to identify suspicious activities, as it lets you pivot from internal data to host-based or third-party sources.
While SOAR is an excellent solution for any organization looking to improve its cybersecurity strategy, it’s important to consider implementing it carefully. Many organizations must fully understand what they are trying to automate to buy technologies with SOAR capabilities. It’s best to start by focusing on critical areas and building sophistication over time.
Reduced Time to Detect
In today’s cybersecurity landscape, keeping up with the increasing volume of alerts from multiple sources can be highly challenging. Moreover, many security teams struggle with analyzing their signals to see whether they are real threats or false positives.
To address this challenge, companies started developing tools and services to help automate incident-handling processes. Initially, these tools were developed to automate ticketing systems and case management processes. However, as time passed, organizations realized they needed a broader cyber-automation solution to help them integrate and automate all the different security tools they used.
This is where SOAR cybersecurity comes in. By integrating with multiple security platforms, SOAR enables teams to work as a unified team so that alerts can be correlated and processed efficiently.
By enabling security orchestration, SOAR also provides analysts with playbooks that automatically execute specific actions when certain events occur. This reduces alert fatigue and allows your team to focus on higher-value work.
While other cyber-automation tools only offer a single entry point, SOAR provides an integrated and flexible environment for analysts to access a broader range of data. This is crucial in quickly identifying and responding to suspicious activity, as it helps analysts easily switch from one dataset to another. This enables them to determine if a particular incident requires further investigation or is just a false positive.
Reduced Time to Respond
SOAR can aggregate data from various security tools and devices, providing security teams with a more comprehensive view of threats. This means that they can respond to incidents more quickly.
In addition, SOAR enables analysts to use playbooks to automate tasks in response events. These playbooks are detailed checklists that execute a specific sequence of actions that an analyst would otherwise perform.
As SOAR automates security processes, it reduces human error and frees analysts’ time to perform higher-value activities that improve incident response. Examples of these actions include managing SSL certificates, diagnosing endpoint agent issues, and managing vulnerabilities.
SOAR also helps filter general alerts from SIEM tools to identify false positives and detect real threats. This helps free security analysts to focus on more important work while reducing their workload and stress levels.
Similarly, SOAR can enable machine learning-driven response (MDR) to disable passwords and devices acting suspiciously on critical networks automatically. This allows an MDR team to respond quickly and mitigate risks by shutting down the pathways hackers could use to reach targets.
Ultimately, SOAR helps organizations respond to incidents more efficiently, enabling them to handle more alerts without hiring additional staff. This helps to significantly reduce the mean time to detect (MTTD) and mean time to respond (MTTR), which can be crucial for limiting the damage an attack can cause.
Reduced Human Error
SOAR is a security tool that helps organizations automate their security operations. It enables security teams to respond faster and more efficiently to cyber threats.
SOAR can help reduce human error by automating repetitive security workflows such as phishing detection and file hash verification. This allows your team to focus on other, more critical tasks.
Another way that SOAR can reduce human error is by minimizing the number of alerts a team receives. Many NG SIEM solutions produce thousands of alarms daily, making it difficult for analysts to respond to all of them.
The SOAR solution can automatically sift through these alarms and prioritize them for the team to act on. This can significantly increase your security operations’ effectiveness and reduce your teams’ time responding to false positives.
The SOAR tool also enables centralized data collection, which can help your security team gain complete visibility into the various events happening on your network and systems. This is an essential step in preventing cyber attacks from happening in the first place. The data is also helpful in cross-referencing with threat intelligence sources to bolster your defenses. SOAR can also help you proactively detect and respond to incidents that have not yet reached your network. This can significantly reduce the likelihood of your organization becoming a victim of an attack.

 Server Wars 2025: Which Hosting Platforms Are Winning for Gamers?
Server Wars 2025: Which Hosting Platforms Are Winning for Gamers?  AI Tools That Make YouTube Shorts Creation Effortless
AI Tools That Make YouTube Shorts Creation Effortless  FAA Web Scheduler – An Effective Tool for Task Management
FAA Web Scheduler – An Effective Tool for Task Management 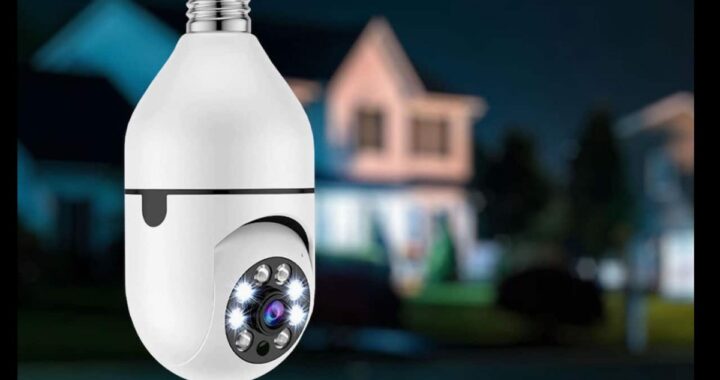 Optiguard: The Smart Security Camera That Fits in a Light Bulb
Optiguard: The Smart Security Camera That Fits in a Light Bulb  What Is SDMC Webnet? A Complete Guide
What Is SDMC Webnet? A Complete Guide  What is a Bluetooth Jammer and How Do I Use it?
What is a Bluetooth Jammer and How Do I Use it?  Movierulz 2026: Risks, Reality, and Safer Alternatives
Movierulz 2026: Risks, Reality, and Safer Alternatives  Top Networking Events in Atlanta 2023
Top Networking Events in Atlanta 2023  Lighten the Mood: Hilarious Work Meeting Jokes
Lighten the Mood: Hilarious Work Meeting Jokes  Exploring Movierulz 2024: Safe Download Tips
Exploring Movierulz 2024: Safe Download Tips